What are they?
Backend cloud services are the operations and routines end users don’t see but are essential to provide resilience and secure access to backend services and resources.
The Problem:
In simple terms the backend services in AWS or within a cloud deployment should allow our frontend services to power up user interfaces and scale to meet user demands. Backend services should also include collating, analysing and sending requested data, meaning telemetry and logging.
The Mesh:
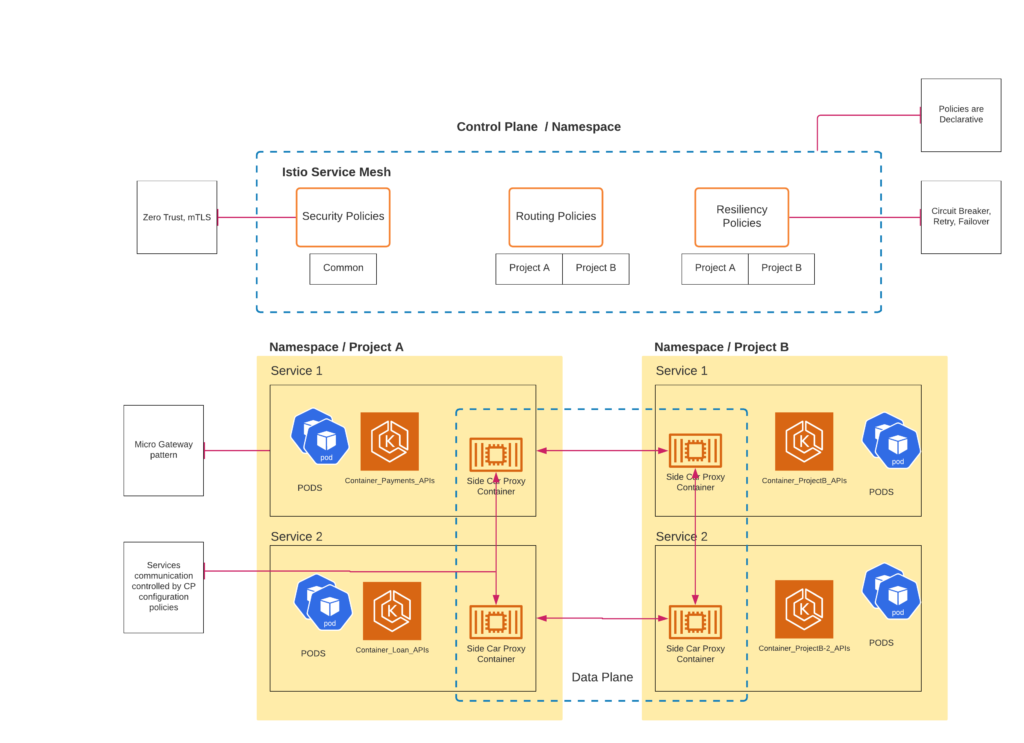
A mesh is a networking convention which is often referred to as east-west traffic management, and the securing of east-west traffic within a platform. This is a key concern when deploying complex scalable systems, usually based on containers, Kubernetes infrastructure and related micro-services.
- Service mesh. Service mesh is a dedicated infrastructure layer for facilitating service-to-service communications between services or microservices.
A service mesh is a way to control how different parts of an application share data with one another. It is also a dedicated infrastructure layer built into an app. Istio is an open-source service mesh, and the major cloud providers have all built their managed offerings. With service meshes, you can manage, observe and secure services without having to change service credentials. They can reduce or eliminate the need to manage service accounts at all.
The AWS App Mesh can manage and monitor microservices. This service offers users control of the communication and network traffic targeting those microservices. When the cloud handles mundane but critical administrative duties of backend services, IT departments and business units are free to take on more involved tasks.
Part of Security:
Meshing and network management is a part of our security posture. We need to secure the storage and distribution of access keys, to operate with the principle of least privilege and to safeguard inter-service communications. By restricting access to a cloud environment, an organization can lower its security risks.
When it comes to digital security in the cloud, there are some key terms to know and understand:
- Service account. This account is used by an application or computer workload, such as a cloud-based app, rather than a person (user account).
- Access key messages. These are long-term credentials, which in AWS are used to sign programmatic requests to the AWS Command Line Interface or AWS API Gateway.
- Digital certificate. This file verifies a user’s or service’s identity and enables encrypted communications.
Managing access to backend services
When building back-end systems and services that need to scale some best practices include:
- Keep the number of people with access to high-level data to a minimum. Follow the least privilege model to permit only the access that’s necessary to the service account.
- Store security keys appropriately. Storing access keys or service credentials in code is unwise. Use an external key vault or secrets manager to encrypt sensitive data, including access keys. For added protection, explore using cloud-based key management systems and hardware security modules.
- Update, rotate or change service account credentials regularly. When API access keys expire before they are updated, that can result in an outage. Update access keys regularly and avoid credentials that never expire.
- Avoid using the same service accounts for multiple services. Be conscious of multiple users sharing accounts. Decommission service accounts when no longer needed. Track all the places where the service accounts are in use.
- Stay current with automated tools. These tools can help take the labour out of managing service accounts to keep backend cloud services secure. Features include automatic renewal of keys or certificates, the cataloguing of service principals and profiling permissions, and managing of privileges assigned to service accounts.
Cloud platforms offer innovations
Most cloud platforms enable users to manage credentials and observe and secure services without changing access keys. Important strategies for securing services and minimizing outages include using an automated certificate management tool, auditing access to services, time-bound access for on-call engineers, and secure key storage.
On AWS, AWS Secrets Manager enables users to rotate, manage and retrieve database credentials, API keys and other secrets through their lifecycle. Temporary security credentials can be configured to expire after a few minutes or several hours.
Managing it all
Managing backend cloud services with the help of providers such as Google, AWS and Microsoft Azure can mean making frontend services appear to be seamless and reliable. There is complexity in password rotations and security certificate expiration dates. Mutual authentication using private certificates can help. Cloud-managed PKI certificates can simplify administrative security tasks. For companies that can use microservices, service meshes can manage much of the infrastructure.