Cloud Digest – August 12 2019
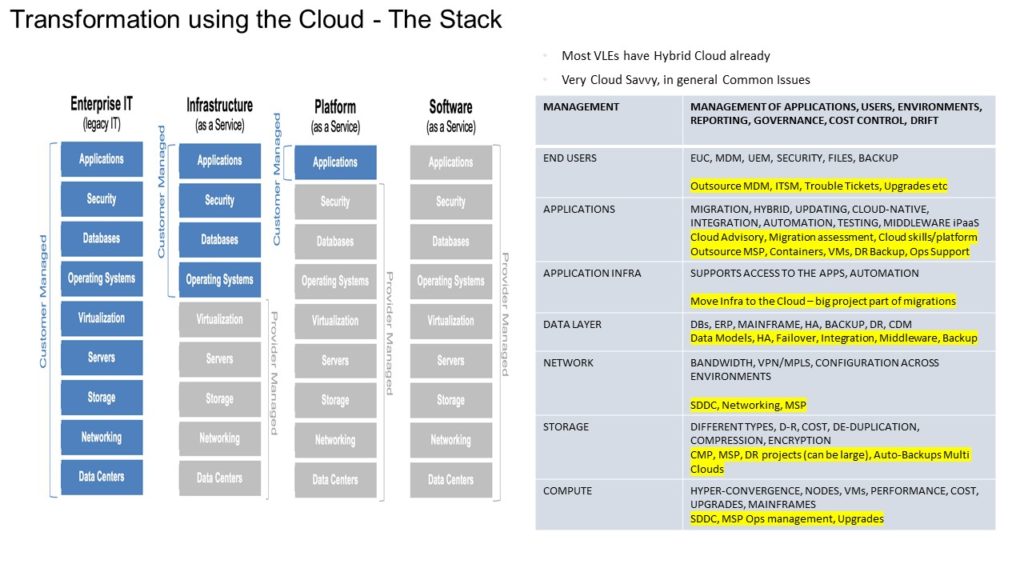
The IT Stack. Cloud computing encompasses the entire IT Stack. This needs to be kept in mind when deploying applications, looking at dependencies, modelling security, assessing non-functional requirements, and mapping out systems integration, testing, coding and deployments. Most firms have a Cloud-governance mess, with silos, sprawl and uncontrolled costs. Configuration drift and not implementing standard best-practices or key principles across environments is also a common issue.
Cloud Architecture(s)
Most VLEs have an incorrect Multi-Cloud strategy (and huge governance messes). It is a fallacy that firms (and their people) can be good at everything, including, multi-clouds…..And when you choose a tool-set or a particular database from a Cloud provider, you are already locked into their platform, so ‘portability’ which is often-touted as a rationale for the Multi-Cloud is in fact a chimera.
“It is an indisputable fact that to be good at just one cloud, never mind many, you have to invest in trained and experienced people, evolved processes, and new tooling and technology. This can cost millions of dollars and months of experience. Some people never get good at one cloud…
1: You will have much higher overheads the more clouds you have
2: The more clouds you have the more shallowly you will experience each cloud.”
How many companies spend the requisite budget on documentation, people, process engineering, tooling, agile-scrum expertise for just one cloud, let alone 2-5? What are the governance and cost implications of Cloud sprawl and impacts on applications, productivity and clients?
Management, Governance
Governing Cloud(s) environments is a critical management concern. Cloud complexity needs to be understood, documented and effectively governed.
“The majority of enterprises have a complexity issue right now, or they will have one by the end of 2020, thanks to disconnected cloud builds or migration teams, and focus on best-of-breed and multicloud architectures. Typically, the drawbacks to this approach are, first, insufficient skills, tools, and budgets to keep a complex cloud deployment running. Later you’ll see outages, perhaps a breach, and high turnover in the cloudops team.
The first step to address your complexity is to examine all the data, services, workloads, and platforms. Look for ways they can be managed using tools that support abstraction and automation.”
Applications
90% or more of Cloud business applications are not fit for the enterprise purpose a recent report finds. Security could also be compromised.
“According to Netskope, this means organisations relying on such applications could be putting both their customer and employee data at risk of exposure to security threats.
Jason Clark, chief strategy officer at Netskope, said the results highlight the need for organisations to make sure they have controls in place to safe-guard data being processed and transmitted by cloud applications.”
Applications Infrastructure
No-Ops – the usage of AI and other automation techniques to reduce manual operational intervention. Though automation will replace inefficient processes, there will always be manual intervention, especially when it comes to patching, upgrades, new version production and testing, amongst many other IT tasks.
Data Layer
An excellent primer on Server-Less Computing. An obvious problem with Serverless, besides vendor-lock in, is time. Serverless code is ephemeral, not suited to long-running tasks. So, the design and rationale for using Serverless within data-event driven architectures is very important.
“For instance, for languages, you can use Node.js, Java, Go, C#, and Python on AWS Lambda, but only JavaScript, C#, and F# work natively on Azure functions. When it comes to triggers, AWS Lambda has the longest list, but many of them are specific to the AWS platform, like Amazon Simple Email Service and AWS CodeCommit; Google Cloud Functions, meanwhile, can be triggered by generic HTTP requests. Paul Jaworski has an in-depth look at the stacks for each of the big three offerings.”
Network-Storage-Compute
Top Storage firms are here. All have Cloud offerings. Cloud networks, affect security and application transformation.
“In the world of cloud-based network security, SDP (software defined perimeter) is like sunshine on a cloudy day. Cloud Security Alliance developed SDP, which is already seen as a disruptive technology, according to network architect Matt Conran. SDPs are similar to zero-trust networks, as all endpoints must go through authentication and authorization processes before accessing the network.
SDP is a naturally cloudy network security framework: It creates two-way encrypted connections so potential bad actors can’t see beyond the connection and perimeter. Because SDP restricts user access to networks, it minimizes a network’s attack surface and, therefore, the amount of damage bad actors could cause, Conran said. While SDP has its flaws, this framework could address several common network security issues.”
Security
Good explanation of how Internet viruses and malware can spread. Infected host applications can transmit the virus to other users through resident and non-resident viruses, boot sector viruses and web scripting viruses.
DevOps
Some firms are pushing the idea of Low-Code, No-Code development. While these buzzwords are hard to define, it essentially means is that non-IT business-people, can use a simple UI and configure code and application functionality to suit a business requirement. Firms that are engaged in providing such services include: Appian, Appsheet, C3, Webalo, Dell Boomi, Jenkins, Pegasystems, Google, Progress, Quick Base, K2, Caspio, Turbo, BettyBlocks, Appery.io and several others.
Containers
Of course, there’s Kubernetes, which orchestrates and manages collections of containers. It was one of the first and best-known examples of projects that make containers truly useful for production use. However, more recently, the container ecosystem has truly exploded. A service mesh like Istio addresses many of the challenges faced by developers and operators as monolithic applications transition towards a distributed microservice architecture. A tracing tool like Jaeger analyzes what’s happening as a transaction moves through a distributed system. Monitoring software like Prometheus captures time-series events for real-time alerting and other uses. Grafeas and Kritis provide security policy attestation and enforcement.
Serverless and Containers work well together.
“Cloud native, put simply, involves using containerized applications and Kubernetes to deliver software in small packages called microservices. This enables developers to build and deliver software faster and more efficiently in a continuous delivery model. In the cloud native world, you should be able to develop code once and run it anywhere, on prem or any public cloud, or at least that is the ideal.
Serverless is actually a bit of a misnomer. There are servers underlying the model, but instead of dedicated virtual machines, the cloud vendor delivers exactly the right number of resources to run a particular workload for the right amount of time and no more.”
AI/Machine Learning
AI, Machine Learning and related data-storage needs.
“AI is a broad term that covers a wide range of use cases and applications, as well as different ways of processing data. Machine learning, deep learning, and neural networks all have their own hardware and software requirements and use data in different ways.
“Machine learning is a subset of AI, and deep learning is a subset of machine learning,” says Mike Leone, senior analyst at ESG.
Deep learning, for example, will carry out several passes of a data set to make a decision and learn from its predictions based on the data it reads.
Machine learning is simpler and relies on human-written algorithms and training with known data to develop the ability to make predictions. If the results are incorrect,data scientists will change the algorithms and retrain the model.”
=END