Overview
AWS has a comprehensive suite of Security Services and an extensive White Paper. You will want to deploy many of these services (they are managed by AWS); along with (depending if you are using an IaaS, PaaS, or blend of both) your own security models (based on your own firm’s Security Principles and Architecture). AWS has partners who have built Security offerings.
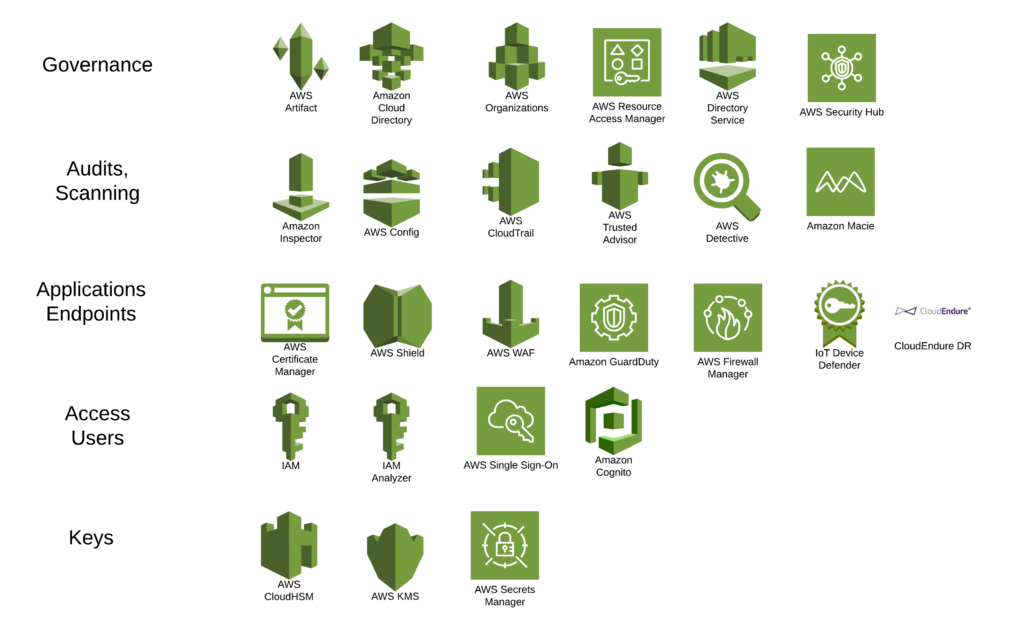
Blue=Governance as well as Security
| Service | Overview | Area |
| AWS Artifact | Compliance, No cost, self-service portal for on-demand access to AWS’ compliance reports | Compliance, Audits, Governance |
| AWS Certificate Manager | Provision, manage, and deploy public and private SSL/TLS certificates | Network |
| AWS Cloud Directory | Organizational charts, course catalogs, and device registries, flexibility to create directories with hierarchies that span multiple dimensions | Governance |
| AWS CloudHSM | Hardware based key storage for regulatory compliance | Access, Keys |
| AWS CloudTrail | Monitors, provides history of access to all AWS resources including SDKs, CLI, Console can detect unusual activity | Monitoring |
| Amazon Cognito | Identity management of all apps, often used with mobile application access | Access, IAM |
| AWS Config | Assesses, audits, evaluates the configuration of the deployed AWS resources | Compliance, Audits |
| Amazon Detective | Incident response, Investigate potential security issues | Incident reporting |
| AWS Directory Service | Integrates with AD, can be integrated on premise or used just in the cloud, allows AD permission-based access to resources (SSO, GPO, Workspaces etc) | SSO |
| AWS Firewall Manager | Centralises the management and deployment of firewall configurations across the AWS accounts | Networks |
| AWS GuardDuty | Monitors the accounts and environments, integrates with CloudTrail and VPC Flows | Environments |
| AWS IAM | Identity and Access Management, SSO for users, roles and groups including MFA, mandatory to set up and use | IAM, Access, Governance |
| AWS IAM Access Analyzer | Based on least privilege provides an overview of resource usage by user and access based on existing policies (eg root vs OU) | IAM |
| AWS Inspector | Checks configuration, security, compliance of existing applications deployed on AWS, can be integrated into DevOps | Environments, Configuration |
| AWS IoT Device Defender | Security management for IoT devices | IoT Access |
| AWS Key Management Service (KMS) | Key storage and management | Access, Keys |
| AWS Macie | Uses Machine Learning to understand patterns of usage, access and threats to sensitive data eg S3 buckets, integrates with CloudWatch | Data |
| AWS Organizations | Automate account creation, create groups of accounts, apply policies to these groups for governance | Environmental Governance |
| AWS Resource Access Manager | Allows sharing of resources across accounts including AWS Transit Gateways, Subnets, AWS License Manager configurations, and Amazon Route 53 Resolver rules resources | Configurations |
| AWS Secrets Manager | Rotate, manage, and retrieve key secrets (access to EC2, environments) | Keys, Access |
| AWS Security Hub | Scans and consolidates security settings, issues, findings across all assets and security services in a centralised location | Reporting, Monitoring, Governance |
| AWS Shield | Infrastructure protection, DDoS protection | Network |
| AWS Single Sign-On | SSO for end users, integrates with AD, access across accounts or applications for users, managed centrally | SSO, Governance |
| AWS Web Application Firewall (WAF) | Filters malicious web traffic | Applications |
| CloudEndure Disaster Recovery | Fast, automated, cost- effective disaster recovery | DR |
For larger firms many of the above services will need to be used. They form part of the overall security model. NIST and CSBP (cloud security best practices) are mapped to these AWS services.
AWS keeps an active Security Blog and should be consulted regularly. An example is from the AWS Security Blog (July 2020); on how to secure data in the AWS Cloud, to meet various compliance and regulatory statutes (SEC and Financial authorities for instance). Many of these ideas are also linked to cost reduction.
Overview Diagram of AWS Security Services
AWS covers a lot of the IT Stack and is focused on providing automation, alerts, integrated monitoring. Clients will still need to develop a Security Model based on who they are; what tools they are using and the types of deployments (IaaS, PaaS, SaaS). Data backup, AMI backup, Code backup, EBS and disk backup are also part of Security. Key data and data types should be backed up within AWS to a 2nd region (the DR-Backup Region) and outside of AWS (in case AWS suffers a fabric failure).