1. Virtual Network (VNet)
What it is: A logically isolated network for your Azure resources — like a virtual version of a traditional on-premises network.
Key Components:
- Subnets (e.g., App subnet, DB subnet)
- IP address ranges (CIDR)
- NSG (Network Security Groups)
- Route Tables
- Service Endpoints
- Private Endpoints
Real-World Example:
You’re hosting a 3-tier web app:
- Web App in App Subnet
- API in Logic Apps/Subnet
- DB in DB Subnet
Use NSGs to allow only API access to DB and restrict all external traffic.
2. Network Security Group (NSG)
What it is: Rules that allow/deny traffic at subnet or NIC level.
Use Case: Allow port 443 only for public access to a web app, while port 1433 (SQL Server) is only open to internal subnet.
3. Azure Firewall vs NSG vs Application Gateway WAF
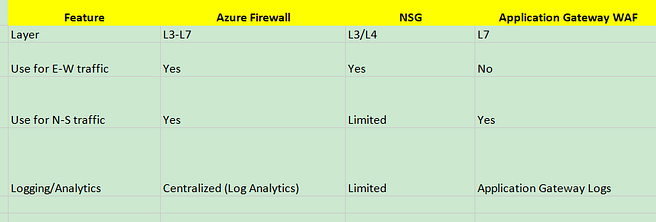
4. Application Gateway (Layer 7 Load Balancer)
With WAF (Web Application Firewall)
- SSL Termination
- Path-based routing
- Rewrite headers, Custom probes
Real-World Example:
Use URL path-based routing to route:
/api/*→ App Service A/admin/*→ App Service B
5. Azure Load Balancer
Types:
- Basic — limited scope, non-zonal
- Standard — zone-aware, HA
Use Case:
Backend VMs in VMSS behind Load Balancer for app scaling.
6. Azure Front Door (Global Anycast CDN + WAF)
- Geo-redundant, works across regions
- Smart routing (latency-based)
- SSL offloading + Caching
Example:
Your web app is deployed in East US and West Europe. Azure Front Door automatically routes Indian users to East US (lowest latency).
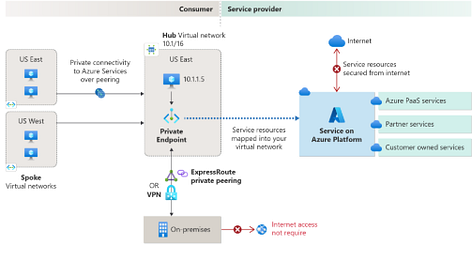
7. Private Link / Private Endpoint
Securely access Azure PaaS (like Azure SQL, Blob, etc.) via private IP.
Use Case:
Your app in VNet needs to access an Azure SQL DB without exposing it to the public internet.
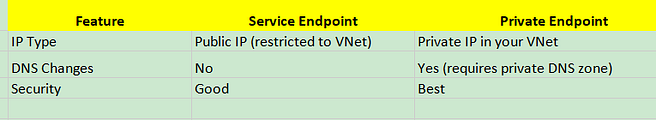
8. Service Endpoint vs Private Endpoint
Service endpoints
Service endpoints extend your virtual network private address space and the identity of your virtual network to the Azure services, over a direct connection. Endpoints allow you to secure your critical Azure service resources to only your virtual networks. Traffic from your virtual network to the Azure service always remains on the Microsoft Azure backbone network.

Azure Private Link
Azure Private Link enables you to access Azure PaaS Services (for example, Azure Storage and SQL Database) and Azure hosted customer-owned/partner services over a private endpoint in your virtual network. Traffic between your virtual network and the service travels through the Microsoft backbone network. Exposing your service to the public internet is no longer necessary. You can create your own private link service in your virtual network and deliver it to your customers.
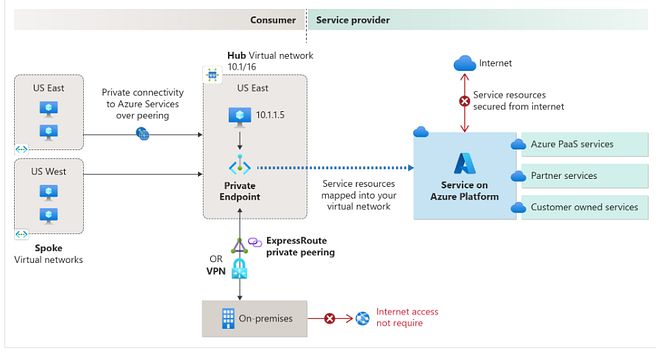
9. ExpressRoute
Private dedicated fiber connection from on-prem to Azure (not over public internet).
Use Case: A bank hosts sensitive apps in Azure but uses ExpressRoute to comply with regulatory needs.
10. VPN Gateway
Site-to-site or point-to-site connection to Azure via IPsec/IKE.
Scenario: Your dev team connects from home via VPN Gateway for secure dev/test environments