PAM and security in general are concerned with 2 basic concepts:
1 ) Protecting my systems and data from external attack and;
2 ) Protecting my systems and data from internal malfeasance or corruption
Though we shouldn’t put too much stock in the ‘pay-to-play’ Gartner group, in Enterprise-Group think, the GG is still used as an oracle and pagan touchstone. In June 2018 the GG listed PAM as the most important security project in the next year. Privileged Access Management is the No. 1 security project to implement in 2018. There are many aspects to security within an IT stack, all of them are important, but protecting data, systems and production access, and logging what engineers are doing against different environments is quite plainly a necessity not a luxury. For many firms it is a regulatory obligation.
PAM – first phase: discovery
- Within the Enterprise the initial focus on PAM should be to secure critical credentials, vaulting keys and passwords; and shutting down attack vectors for hackers. The following steps will aid Enterprises to accomplish this;
- Evaluate privileged accounts for your data storage and understand ‘privileged access’ means, by understanding your data, persistent and ephemeral storage of data, and access to that data.
- Make sure your critical app and business data is backed up and you have a reasonable (cost-effective, well documented and though out) disaster-recovery plan. This includes code, business app data, access keys or system access controls.
- Evaluate your environments including development, QA, Pre-Prod and Prod. Who has access and why? Do Dev Engineers have RBAC to Prod? If so why indigenerics.com? Map out roles, groups and access and identify who SHOULD have access to your environments.
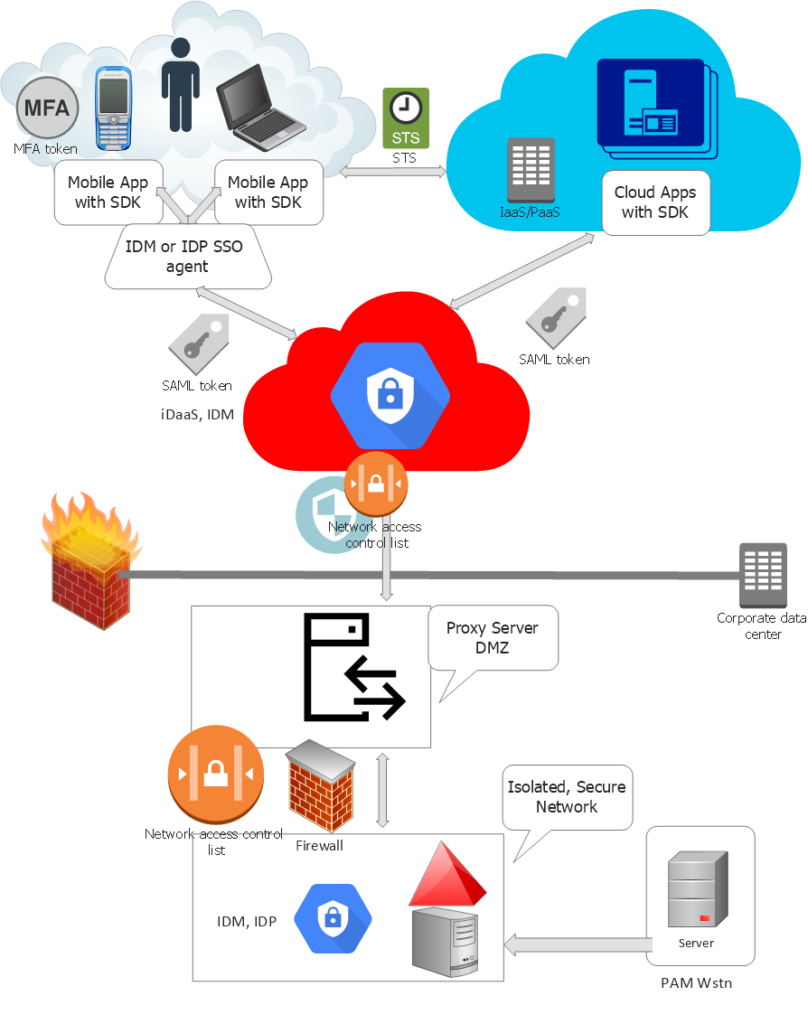
- Identify the difference between human PAM access and application (SSO, SAML, OAuth) access. Within SSO the SDKs must have encrypted keys, and with OAUTH security tokens are used. Understand how these are issued and controlled and what role access is valid for the applications. For human access to sensitive environments, turn on MFA.
- Once you have performed the above, select a PAM solution that best fits your enterprise requirements and particular architecture (on-premise, cloud, hybrid). Training and POCs will be needed. Budget for it, and budget for a never-ending PAM security life-cycle.
- Once the PAM is selected ensure that it has automated discovery of all users, access, flows and other parameters. This dynamic scanning tool will update your documentation and be able to report key metrics.
PAM – second phase: security lifecyle
PAM and security never end. There is no ‘one project’ as GG suggests. Security should be an onsite critical full time role, in which the CISO and his group are involved in all projects. Templates, principles, reviews and audits are mandatory. The PAM life-cycle includes:
Define, Classify, Design privileged account management
In phase one you have established what is PAM. Security policies are now necessary to develop to form acceptable use case guidelines for privileged account access. This includes the principle of ‘Least Privilege’ access (see below). This should take the form of a high to low level design document, using UML notation, process notations, and work-flows. This should conform to NIST and OWASP and be detailed. It will end up being an end to end Security model design.
For example, a use case might be setting up access roles and policies for the role user ‘development engineer’, to access only ‘certain’ dev environments, but being default-denied for other environments. You then need to identify how to do this, where to store the role and key information, and how to revoke or grant access and manage users and groups.
Turn on Automated Discovery
Once security policies and RBAC are created, the automated PAM scanning tool should be monitored by a Security SME to enforce compliance, spot threats or smooth out processes that may need adjustment.
Manage and protect PAM passwords
Proactively supervise and control privileged account access with password protection software built into the PAM solution. PAM should automatically discover and store privileged accounts; scan individual privileged session activity; schedule password rotation; and examine password accounts in order to quickly detect and respond to malicious activity.
Limit IT admin access to critical systems
Develop a least-privilege strategy so that privileges are only granted when required and approved. Enforce least privilege on endpoints by restricting end-users configured to a standard user profile and automatically elevating their privileges to only to run approved and trusted applications.
For IT administrator privileged account users, control access and implement super user privilege management for Windows and UNIX systems to prevent attackers from running malicious applications, remote access tools, and commands. Proper PAM solutions offer least-privilege and application control to enable seamless elevation of approved, trusted and whitelisted applications while minimizing the risk of running unauthorized applications.
Monitor and record sessions for privileged account activity
The PAM solution should be able to log key strokes, take video, record session time and usage. This will enforce proper behavior and helps avoid end-user errors because the activities are being supervised. If a breach does occur, monitored privileged account use also provides information to forensics teams to assist in identifying breach causes as well as provides intelligence toward reducing future risk exposure.
Detect usage and analyze behavior to comb for abnormalities
Real-time visibility into the access and activity of PAM users will help negate account compromise and potential insider threats (eg the rogue engineer who is angry at being passed over for promotion). Behavioral analytics use data to establish individual user baselines, such as user activity, password access, and time of access. This information is used to identify unusual or abnormal activity to predict threats and alert IT teams when they occur.
Respond to breaches
When an account is breached, changing the password or disabling the account is probably ineffective. If penetrated and compromised by an outside attacker, the hacker can quickly install malware, disable accounts, lock-down environments, deny environment access and even create their own privileged accounts. If a domain administrator account is taken over, you should assume that your entire Active Directory is vulnerable. A IR plan is needed including details on who, how, what, when and approvals being needed for any action that may be considered high risk.
Review and audit privilege account activity.
PAM must supply automated reporting to track the cause of any security incidents and comply with industry and government regulations. Auditing of privileged accounts will also provide cybersecurity metrics to show other executives quantified information to make better informed business decisions.
Happy PAMing.
===END