Security of VMs and Applications located at AWS. Example architecture with practical security. Conforms to NIST and Cloud Security Best Practices. Perimeter, Applications, Network, and Data Access are secured.
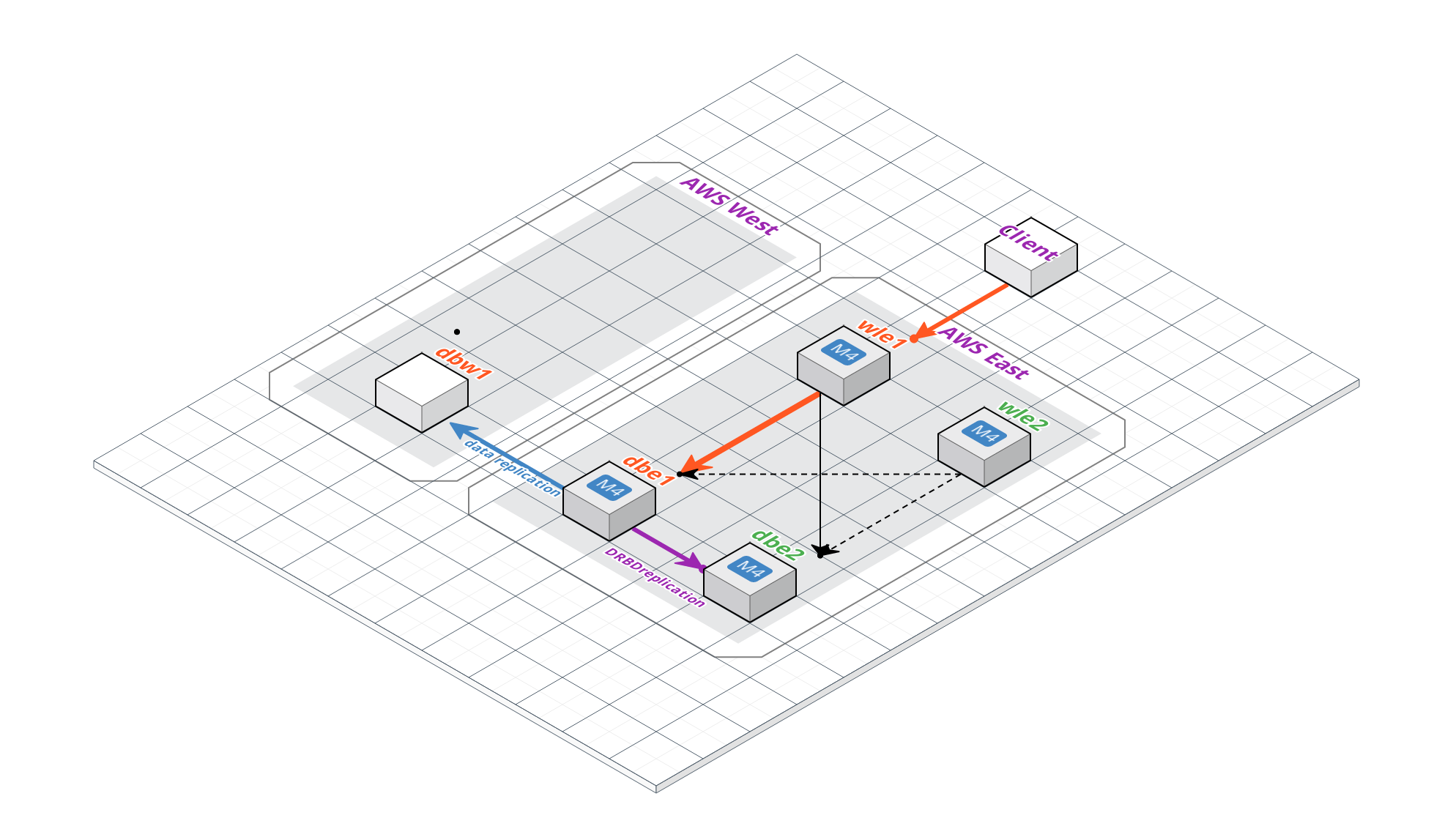
Network security
Port filters
- Only specific IP ports are allowed for external access from Global Network.
- These are SSH (22), HTTPS (443), HTTP (80).
- SSH is secure encrypted protocol that is used only for system administrators access.
- HTTPS is secure encrypted protocol that is used for user application communication.
- HTTP is not secure, not encrypted protocol that is immediately switched to HTTPS as soon as user’s browser tries to reach HTTP. HTTP is open only for user convenience.
- FTP (20,21,47304) is open only for access from Corporate IP 216.aa.bbb.55.
- All other ports are closed, including ICMP (ping, traceroute).
- There are two levels of port filtering:
- AWS network policies
- System Firewall
Application Server certificate and traffic encryption
- Domain name yyyy.com is secured by certificate registered at trusted certificate authority.
- All browsers have certificate verification capabilities. The site with correct certificate will have “Green Lock” icon near URL, that indicates the site is verified and trusted.
- All user’s traffic goes via HTTPS only and is encrypted.
- Browsers use HTTPS. When they try to enter via HTTP, they are automatically switched to HTTPS by the web application.
- Application uses HTTPS and certificate verification as well.
- It is safe to access web applications from public networks.
User application access
- Users access the application portal using browsers via HTTPS.
- Users are authenticated by usernames and passwords. It is important for users to use strong passwords.
- We are planning to implement passwords complexity policy in next versions of the application.
FTP application access
- Users synchronizes required data from AS400 database to app database via files transfers.
- There are some limitations of AS400 to use contemporary encrypted protocols (like SSH).
- Files are transferred via FTP protocol, that is not encrypted.
- To mitigate this vulnerability, access to FTP is allowed only from Corporate IP aa.bbb.55. This is set by AWS IP filter policy and system firewall.
System administration access
- System administrators access systems only via SSH using RSA keys and strong passwords.
Attack detection and prevention
System attack detection
- Special system software monitors unsuccessful attempts to login to SSH protocol and blocks an attacker IP for couple of hours after several unsuccessful attempts.
Application attack detection
- Special system software monitors unsuccessful attempts to login to the application and blocks an attacker IP for couple of hours after several unsuccessful attempts.
- Corporate IP will be never blocked because that would cause blocking of all other users working from office.
Rootkit/virus detection
- Special system software monitors possible rootkits/virus’s installations and alerts system administrators if this is detected.